· Compliance · 3 min read
Documentation for Compliance: SOC2 and ISO 27001 Visuals
This guide explains how compliance diagramming with AI turns a stressful scramble into a predictable process by keeping architecture documentation up-to-date automatically.
“The auditors are coming next month.”
That sentence strikes fear into the heart of every CTO. It means you have to stop building features and start digging up “evidence.”
Auditors for SOC2, ISO 27001, or HIPAA don’t just take your word for it that you are secure. They want proof. They want documentation. Specifically they want System Architecture Diagrams.
And they want them to be current.
If you hand them a diagram dated 2019 they will flag it. They will ask “Does this reflect the new payment service you deployed last week?”
This guide explains how compliance diagramming with AI turns a stressful scramble into a predictable process.
The “Evidence” Problem in Audits
Audits are about proving control.
Auditors need proof of current architecture
You need to show that you know what your system looks like. If you don’t have a map you can’t secure the territory.
An accurate diagram proves that you have oversight. It shows that you know where the firewalls are. It shows that you know which database holds the customer data.
The risk of outdated screenshots
The worst thing you can do is fake it. Taking a screenshot of an old whiteboard and putting it in a PDF is risky.
If the auditor interviews a developer and the developer describes a different system than the one in the diagram you get a “Finding” (a fail mark). Consistency is key.
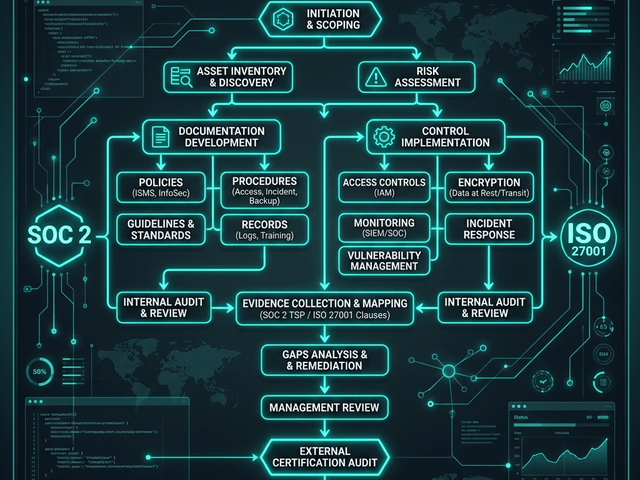
Essential Diagrams for Compliance
You typically need three types of visual evidence.
System Boundaries
This shows the perimeter. What is “In Scope” for the audit? What is “Out of Scope”?
You draw a box around your production environment. Everything inside needs to be secured. Everything outside is third-party.
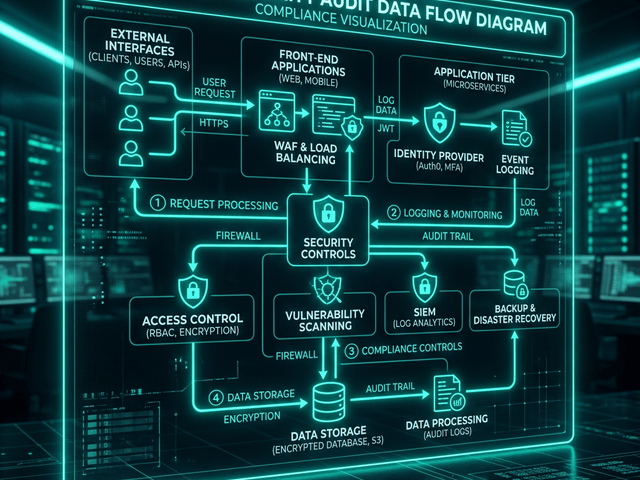
Data Flow Diagrams (DFD)
This tracks the data. Where does the PII (Personally Identifiable Information) go?
You map the flow from the user to the API to the encrypted database. You label the encryption at rest and in transit.
Network Topology
This shows the infrastructure. VPCs. Subnets. Firewalls. Load Balancers.
It proves that your database is in a private subnet and not accessible from the public internet.
Using AI to Generate Fresh Evidence
Instead of manually drawing these every year generate them from your current knowledge.
”Regenerating” diagrams right before the audit
Sit down with your Tech Lead. Describe the current stack to AI Diagram Maker.
“Production environment. AWS VPC. Public Subnet has ALB and NAT Gateway. Private Subnet has App Servers and RDS. S3 Bucket is encrypted.”
Generate the fresh diagram. Date stamp it.
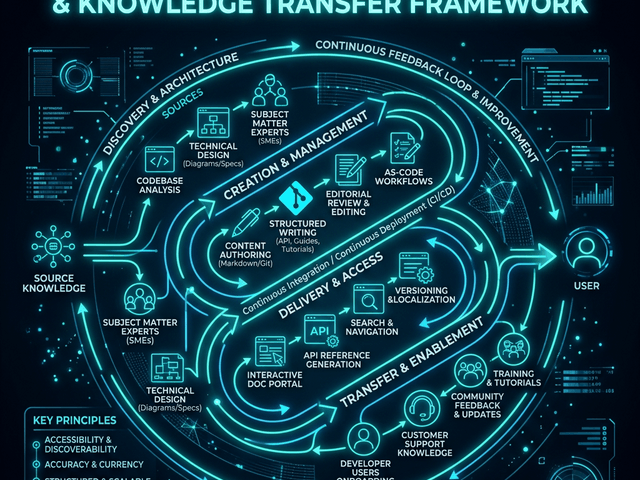
Version controlling evidence (Git workflow)
Save the text description in your compliance repo.
Next year when the auditor comes back you just check the diff. “Did we change the VPC?” “No.” “Okay regenerate the diagram with today’s date.”
Reducing the Stress of Compliance Season
Compliance shouldn’t paralyze your team.
By treating diagrams as code you make them easy to update. You turn “evidence collection” from a month-long project into a standard part of your sprint. You give the auditors exactly what they want: clarity and accuracy.