· Glossary · 2 min read
What Is a JWT (JSON Web Token)?
Learn what a JSON Web Token (JWT) is, how it works, and why it's the standard for stateless authentication in modern web applications.
In the old days when you logged into a website the server created a “Session” and stored it in memory. It gave you a cookie ID.
But if you have 10 servers you have to sync that session across all 10. That is hard.
JWT solved this by making the user carry their own ID card.
Simple Definition
JWT stands for JSON Web Token. It is an open standard (RFC 7519) that defines a compact and self-contained way for securely transmitting information between parties as a JSON object.
Think of it like a digital passport. It is issued by the server. The user holds it. Every time the user makes a request they show the passport.
The server doesn’t need to check a database to verify it. It just checks the digital signature on the passport. This makes it “Stateless.”
Compact, URL-safe means of representing claims
Because it is stateless it scales infinitely. You can have 1000 servers and none of them need to talk to each other to verify the user.
Structure
A JWT has three parts separated by dots. aaaaa.bbbbb.ccccc
- Header: The algorithm used (e.g. HS256).
- Payload: The data (User ID, Role, Expiration Date).
- Signature: The security seal.
Visualizing
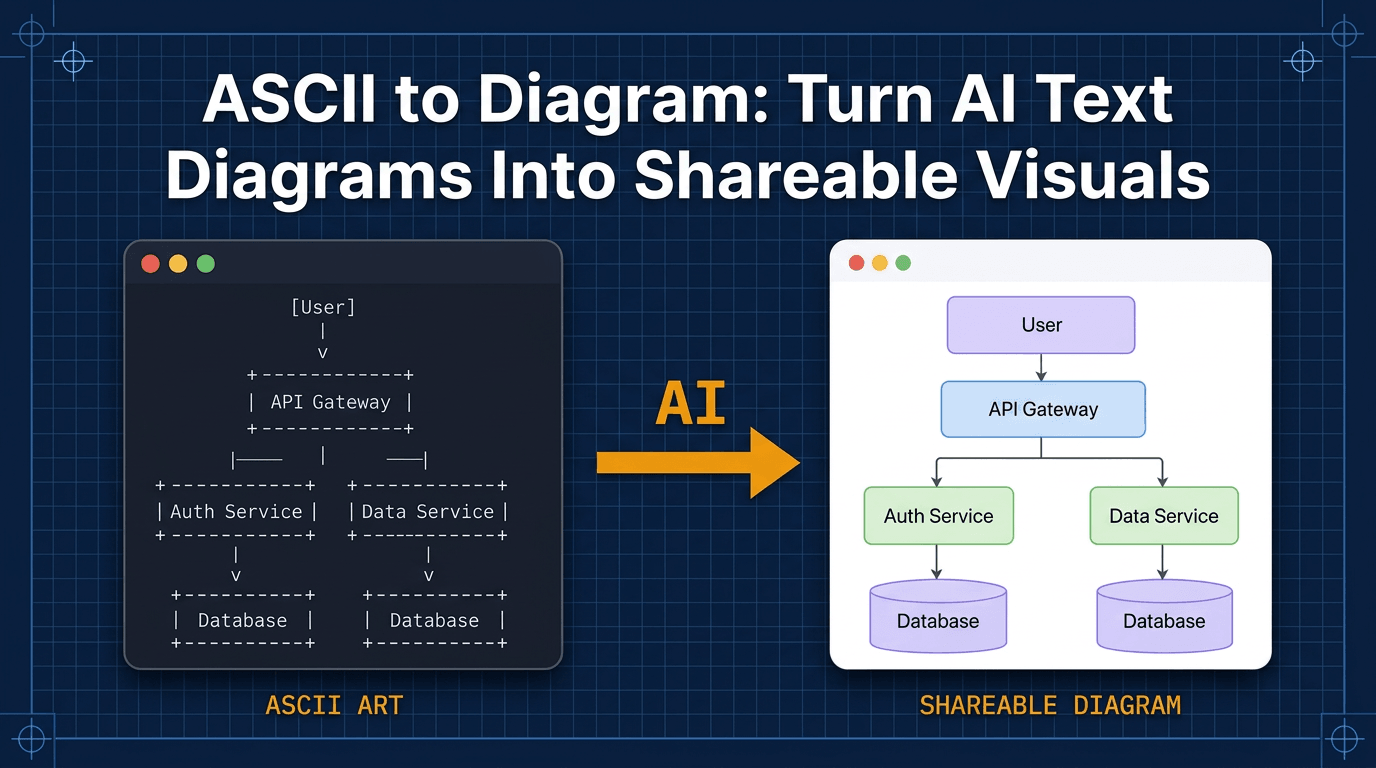
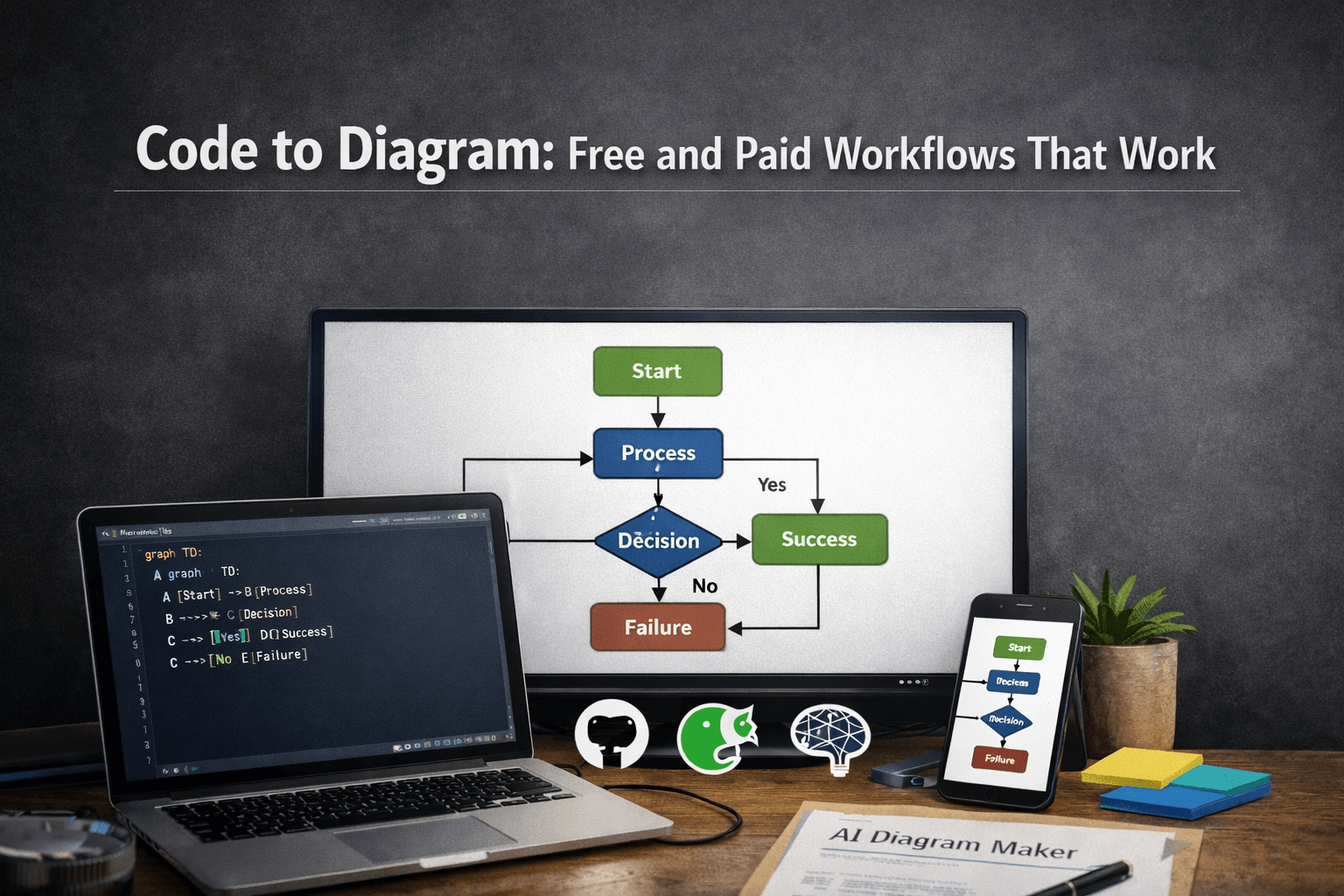
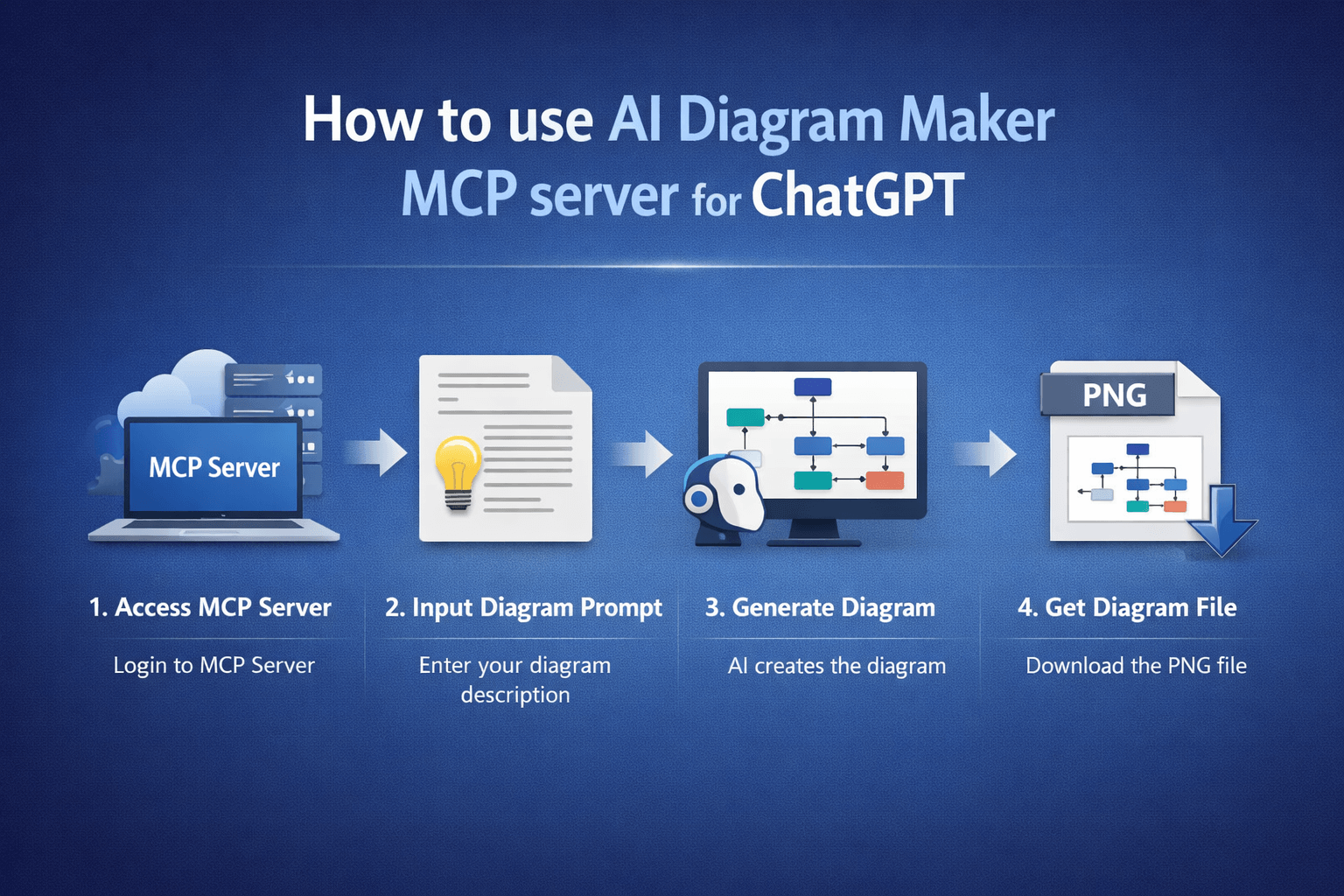
How do you show this flow?
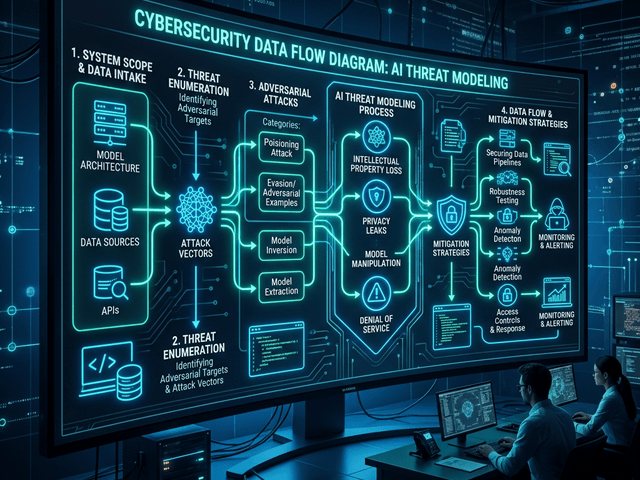
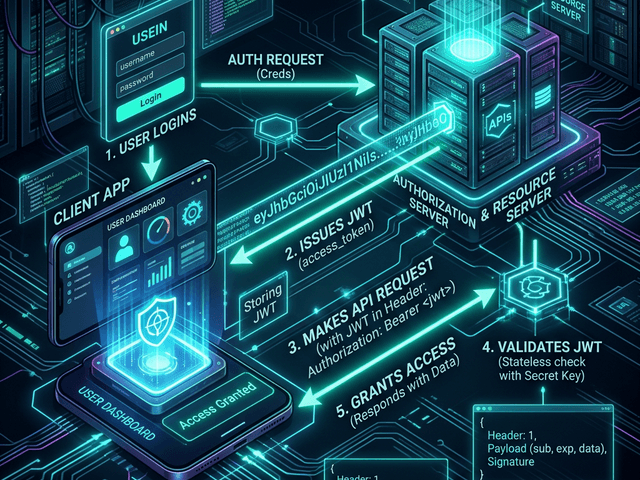
Auth flow diagram
In a Sequence Diagram you show the token exchange.
- User sends Credentials.
- Server returns JWT.
- User sends Request + JWT in header.
- Server verifies Signature.
- Server returns Data.
Visualizing this confirms that you are not sending credentials on every request.
Related Terms
To secure your apps you need these terms:
- Stateless Authentication: A method where the server stores no session data.
- OAuth 2.0: A protocol for authorization that often uses JWTs as the token format.
- Encryption vs Signing: JWTs are usually Signed (tamper-proof) but not Encrypted (visible to anyone). Don’t put passwords in a JWT.
- Claims: The pieces of information asserted about a user (like “Role: Admin”) inside the token.
For more on visualizing security architecture check out our System Design Guide.